Funds collected by ransomware assaults fell to $456.8 million in 2022 from a excessive of $765.6 million in 2021, in line with a brand new report from analytics agency Chainalysis.
Crypto-related ransomware assaults have seen a steep fall in success price over the past 12 months.
Crypto ransomware exercise
The chart under reveals the rise and fall of funds acquired by way of ransomware assaults over the previous 6 years. A dramatic improve was seen in 2020 as stolen funds hit $765 million, with 2021 seeing comparable quantities stolen by dangerous actors.
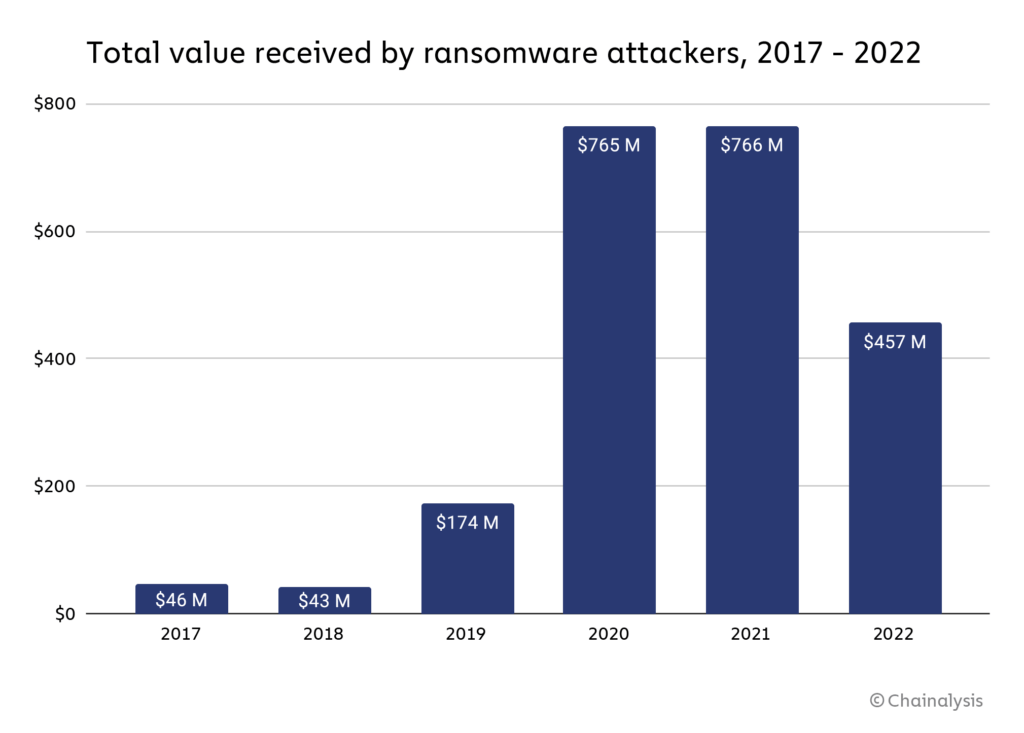
Whereas the Chainalysis report acknowledged that “the true totals are a lot greater” as it’s probably that there are addresses owned by ransomware attackers that haven’t but been recognized, the autumn signifies victims have gotten clever to such assaults. In consequence, Chainalysis made an announcement supporting this sentiment.
“[Ransomware payments falling] doesn’t imply assaults are down… We imagine that a lot of the decline is because of sufferer organizations more and more refusing to pay ransomware attackers.”
Ransomware Strains explode
Though funds to take away ransomware have fallen dramatically, the variety of ransomware strains exploded in 2022. A pressure is a sort of ransomware with widespread variants: Royal, Ragnar, Quantum, Play, Hive, and Lockbit.
Fortinet, a number one cybersecurity {hardware} and software program firm, reported over 10,000 distinctive strains lively all through 2022.
Strains have a reducing lifespan as dangerous actors proceed to fluctuate assault vectors to optimize the amount of stolen funds. For instance, in 2012, strains lasted 3,907 days, whereas in 2022, the typical size was simply 70 days. In consequence, cybersecurity options should sustain with an growing variety of lively strains of their protection technique.
Ransomware funds
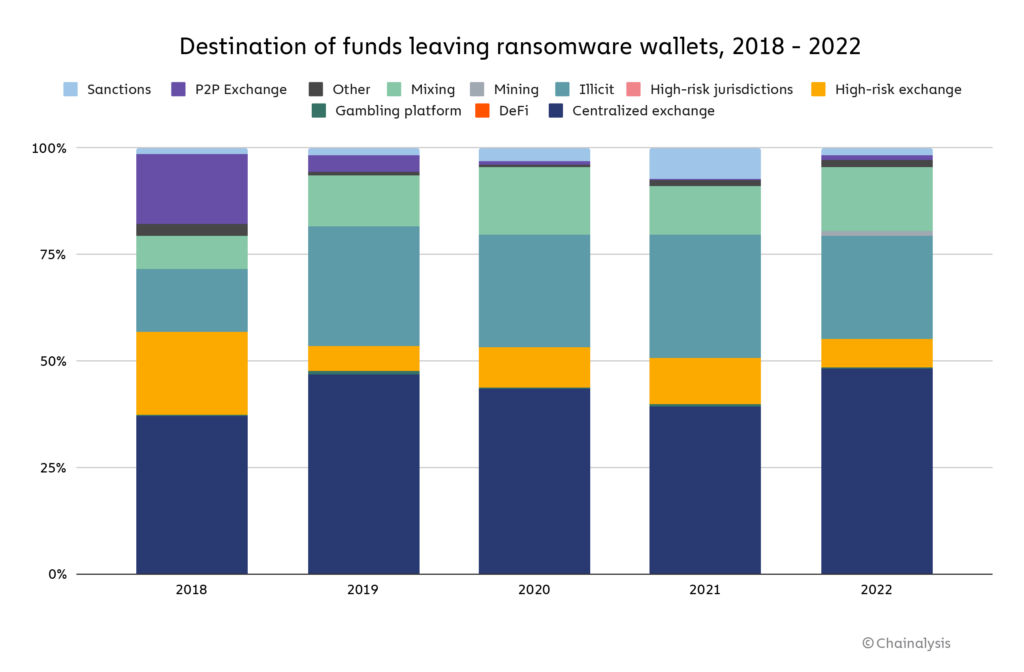
Funds acquired by way of ransomware assaults are laundered by way of a number of avenues. The vast majority of funds are nonetheless despatched to fashionable centralized exchanges. Nevertheless, P2P exchanges, a preferred resolution for ransomware attackers in 2018, now make up a tiny proportion of the general quantity.
After centralized exchanges, a persistent methodology of laundering funds is utilizing darknet markets designated as ‘illicit’ within the Chainalysis chart under. Lastly, mixing providers make up the subsequent most significant slice, permitting attackers to ‘wash’ crypto with little recourse from international authorities.
On-chain information forensics
Chainalysis used on-chain information to establish “affiliate” markets for ransomware software program whereby third events obtain a “small, mounted reduce of the proceeds” in a ransomware-as-a-service mannequin.
“We are able to consider it because the gig financial system, however for ransomware. A rideshare driver could have his Uber, Lyft, and Oja apps open directly, creating the phantasm of three separate drivers on the street — however in actuality, it’s all the identical automotive.”
On-chain information has allowed corporations like Chainalysis to hint dangerous actors throughout the blockchain and presumably establish the subsequent assault vector. For instance, Conti, a prevalent ransomware pressure, was disbanded in Might 2022. But, on-chain information has revealed that wallets linked to Conti are actually shifting onto different strains comparable to Royal, Quantum, and Ragnar.
Ransomware attackers “re-used wallets for a number of assaults launched nominally below different strains,” making tracing exercise comparatively elementary.
Decline in ransomware funds
The variety of profitable ransomware assaults fell because of the elevated understanding of the panorama, improved safety measures, and higher on-chain forensic capabilities. In consequence, victims are refusing to pay attackers, as many are linked to OFAC-sanctioned events.
In 2019 simply 24% of victims refused to pay, whereas, in 2022, the proportion elevated to 59%. Paying a ransomware bounty to a celebration on the OFAC sanctions listing may now be “legally riskier.” Allan Lisk, an intelligence analyst at Recorded Future, informed Chainalysis;
“With the specter of sanctions looming, there’s the added risk of authorized penalties for paying [ransomware attackers.]”
The results of not paying ransomware calls for can typically devastate the victims, who typically lose entry to important information. Nevertheless, because the illicit business turns into much less financially viable, the hope is that the variety of assaults additionally falls, thus lowering the variety of victims.
Regardless, the function of cryptocurrency in ransomware assaults is obvious. It’s a methodology to steal a whole lot of thousands and thousands of {dollars} value of crypto annually. Nevertheless, that’s not to say that there isn’t extra misplaced to conventional monetary belongings, lots of which aren’t traceable by way of a blockchain.

