Understanding open-source protocols
Open-source protocols have grow to be a mainstay within the tech world and are gaining traction as a result of myriad advantages that they provide over their proprietary counterparts.
The protocols are sometimes created with the intention of being utilized by the general public, enabling anybody to look at, alter and share their code. The advantages of open-source protocols are multifaceted, starting from their inherent transparency to their wider accessibility.
Moreover, they depend on peer evaluations, an economical and inclusive mannequin that distinguishes them from their proprietary counterparts. Distinguished examples of open-source software program embody broadly used working methods equivalent to Linux and Android and the favored Firefox internet browser.
Relating to open-source cryptographic protocols, the Bitcoin, Ethereum, Cardano and Polkadot networks stand out as noteworthy blockchain protocol exemplars, amongst others.
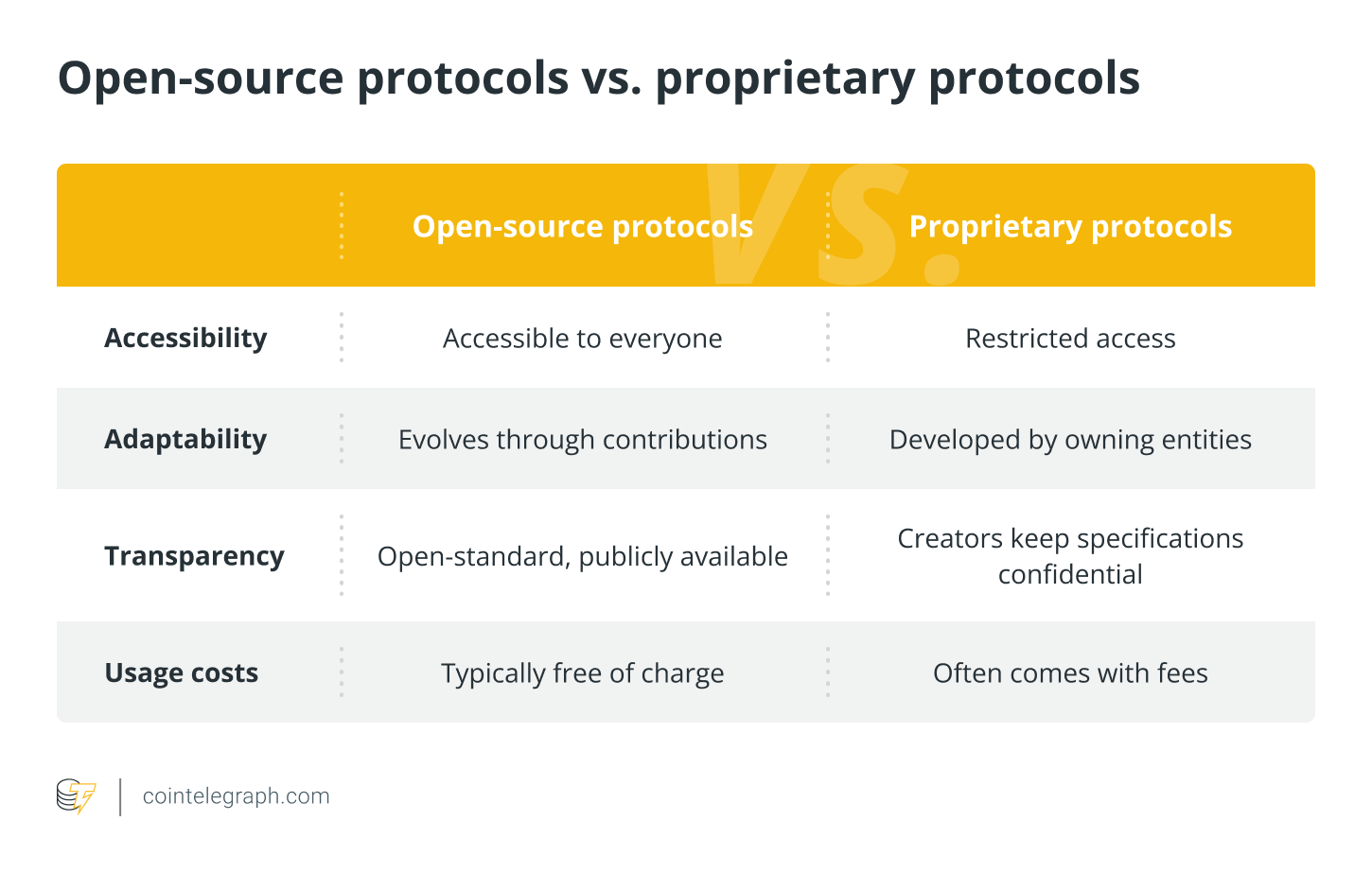
Open-source vs. proprietary protocols
Open-source and proprietary protocols signify two distinct approaches to protocol improvement, every with its personal set of rules on the subject of protocol implementation.
The next is a dissection of their key disparities:
What’s the event course of for open-source protocols?
The event of open-source protocols entails a number of distinct phases, every integral to a protocol’s evolution. All of it begins with the conceptualization section, the place builders lay the muse that defines the protocol’s requirements and goal.
Often, the essential idea is predicated on an current protocol with some enhancements. The conceptualization stage acts because the bedrock, upon which builders meticulously define the structure and options, forming a sturdy theoretical basis. On this section, builders chart out a well-defined roadmap, akin to a strategic plan, guiding the challenge’s trajectory.
The next step within the improvement course of is normally the prototyping stage. On this stage, builders create a useful mannequin of the protocol that features the important thing proposed options. The prototype is normally made accessible to the general public because the beta model.
Releasing the beta model topics the software program to real-world situations and person interactions, permitting builders to discern its strengths and weaknesses. The stage additionally permits builders to get suggestions from the open-source group concerning potential new options to include earlier than the ultimate protocol is launched. Subsequently, the stage is aptly known as the beta testing or person acceptance testing (UAT) stage.
Steady suggestions and updating be sure that the protocol stays aware of the evolving wants and expectations of its person base. After related protocol upgrades are carried out to resolve most of the recognized stability and reliability points, the protocol reaches a degree of stability warranting the designation of a “secure launch.” The secure launch model is normally as dependable as builders could make it.
Nonetheless, the method doesn’t culminate in secure releases. Open-source initiatives require ongoing protocol upkeep. The method normally entails releasing bug fixes, equivalent to safety patches, and updating the code for enhanced compatibility.
Are open-source protocols copyrighted?
When a developer publishes their code as open-source, they’re sharing it with the general public, permitting others to make use of, modify and distribute it. Nonetheless, the act of constructing the code public doesn’t translate to unrestricted utilization.
Copyright legal guidelines apply right here, simply as they do for proprietary software program. The legal guidelines mechanically safeguard any unique artistic work, together with open-source protocols, granting the software program creator unique rights to manage their use and distribution.
Relating to open-source protocol licensing, the developer sometimes attaches a license to it, which acts as a set of tips that clearly delineates what’s permissible and what’s off-limits in regards to the code.
Open-source licenses usually grant customers in depth permissions without having specific approval from the unique writer. That stated, there are two fundamental sorts of open-source licenses: permissive and copyleft.
A permissive license, typically additionally known as a BSD-style or Apache-style license, imposes minimal necessities on how the software program might be modified or redistributed. Nonetheless, initiatives that use this kind of license are obliged to append a guaranty disclaimer. A basic instance of a permissive license is the MIT License. The license permits anybody to make use of, modify and distribute the code with out prior consent.
Tasks using MIT-licensed code sometimes should incorporate the unique copyright discover and a disclaimer explicitly stating that the software program comes with none guarantee. The disclaimer clarifies that the copyright holders bear no duty for any claims or liabilities stemming from the software program’s use.
The license is exceedingly permissive and is crafted to supply most freedom to builders, even allowing the code’s inclusion and distribution in business merchandise.
Relating to copyleft licenses, initiatives that use them are additionally required to affix a legal responsibility disclaimer. They arrive with extra restrictions, particularly in regards to the distribution of modified protocol variations. As an example, the copyleft GNU Common Public License (GPL), a broadly employed open-source license, ensures that the software program stays open and free. Just like the MIT License, the GPL mandates a guaranty disclaimer.
Copyleft licenses assure that open-source protocols or software program might be utilized, tweaked and shared with out constraints. Nonetheless, any modified work should adhere to the identical phrases, preserving the protocol’s openness in all future variations.
Relating to proprietary protocols, the panorama adjustments dramatically. The protocols impose stringent limitations on their protocol documentation, which regularly embody restrictions on modifying or reverse-engineering the code.
To uphold protocol safety, proprietary initiatives normally embody confidentiality clauses of their licenses, stopping customers from disclosing their protocols’ workings or any proprietary data they could come throughout.
When it comes to value, permissive and copyleft licenses are free, permitting customers to make use of and distribute the software program with out cost. In distinction, proprietary licenses usually require customers to pay for entry to and use of the software program.
The way forward for open-source protocols
Because the world turns into more and more digital and interconnected, open-source protocols are poised to play a key position in enabling innovation, particularly on the subject of supporting interoperability amongst totally different methods, functions and units.
The shift is pushed by the widespread, concurrent utilization of protocols crafted by totally different builders on an on a regular basis foundation. Because of this, open-source protocols, particularly those who permit alterations by third events and assist interoperable methods, are sure to take middle stage within the new technological frontier.
Going by present developments, open-source initiatives are additionally more likely to deal with sustainability, vitality effectivity and problem-solving in alignment with the worldwide push for eco-friendly technological options.
Moreover, open-source networking protocol initiatives are anticipated to proceed creating peer-to-peer (P2P) web protocols. The protocols facilitate direct communication between methods, eliminating the necessity for centralized middleman methods. P2P protocols boast an increasing array of functions, significantly in enabling P2P transactions and communications by way of decentralized protocols.

